Introduction: The Perimeter is Dead
Zero Trust Architecture Implementation Strategy by twenty years, the cybersecurity industry operated on a flawed metaphor: the castle and the moat. We built massive firewalls (the moat) and assumed that anyone inside the corporate network (the castle) was trustworthy. If an employee connected to the corporate Virtual Private Network (VPN), they were granted broad access to the entire internal network.
In 2026, the castle has burned to the ground. Your applications are in AWS and Azure. Your employees are working from coffee shops in Bali and apartments in London. Your data lives in Salesforce and Microsoft 365. There is no perimeter left to defend.
When a hacker compromises a single set of VPN credentials today, they don’t just breach one machine; they gain the keys to the kingdom. Lateral movement is the root cause of every major ransomware catastrophe of the modern era. To stop this, organizations must pivot entirely. You must adopt a framework where trust is never implicitly granted based on network location. You must build a Zero Trust Architecture Implementation Strategy.
This comprehensive, 3,600-word guide is not a theoretical overview. It is a highly technical, step-by-step Zero Trust Architecture Implementation Strategy designed for enterprise architects, covering identity providers, micro-segmentation, continuous telemetry, and legacy debt eradication.
The Core Tenets of the NIST 800-207 Framework
Before deploying software, we must define the physics of our new environment. A true Zero Trust Architecture Implementation Strategy is anchored in the NIST SP 800-207 standard, which dictates three absolute truths:
- All data sources and computing services are considered resources. (A smart bulb in the breakroom is treated with the same skepticism as a database server).
- All communication is secured regardless of network location. (Internal “East-West” traffic must be encrypted via mTLS, just like external “North-South” traffic).
- Access to individual enterprise resources is granted on a per-session basis. (Authenticating at 9:00 AM does not mean you are trusted at 2:00 PM if your context changes).
If your current Zero Trust Architecture Implementation Strategy does not meet these three criteria, you are simply doing “rebranded VPN management.”
The Architecture Breakdown: ZTNA vs. Traditional VPNs
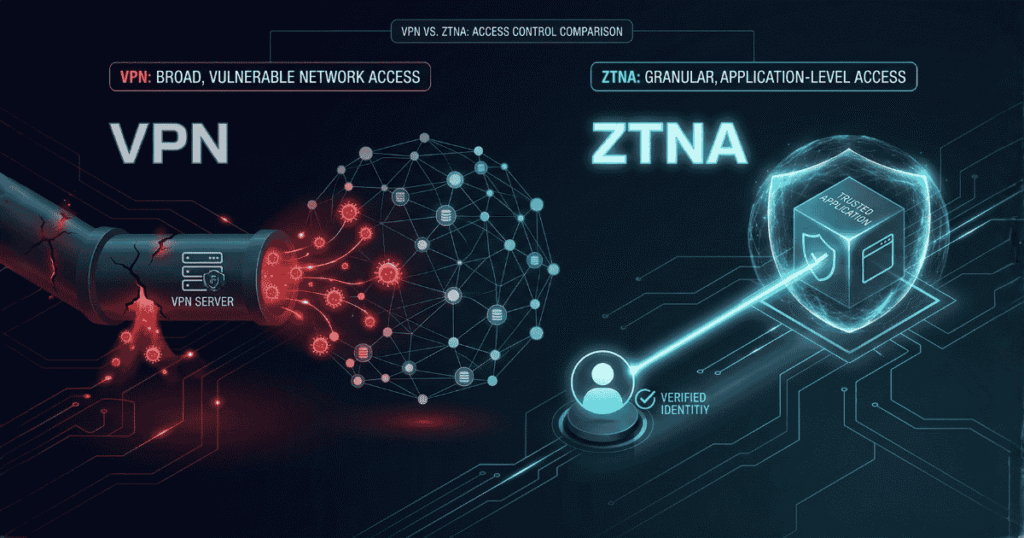
Comparing traditional VPN vulnerabilities to modern Zero Trust Network Access ZTNA routing.
To convince stakeholders to fund your Zero Trust Architecture Implementation Strategy, you must articulate the technical failure of the VPN.
The VPN Flaw (Network-Centric): A VPN connects a user to a network. Once authenticated, the user receives an IP address on the internal LAN. Unless you have painstakingly configured thousands of internal firewall rules (which almost no one maintains properly), that user can ping, scan, and access any server on that VLAN. If the user’s laptop has a silent malware infection, the malware now has a bridge directly into your data center.
Zero trust security for full protection and data safety outline diagram
The ZTNA Solution (Application-Centric): Zero Trust Network Access (ZTNA) connects a user to a specific application, completely obscuring the underlying network.
- The user’s device talks to a ZTNA Trust Broker (hosted in the cloud).
- The internal application talks outbound to the same Trust Broker via a lightweight connector.
- The Trust Broker stitches the connection together only for that specific application protocol (e.g., port 443 for a web app).
- The Result: The user never gets an IP address on your network. They cannot ping the server. The server is completely “dark” to the open internet. You cannot hack what you cannot route to.
The Identity Pillar (The New Perimeter)
In a Zero Trust Architecture Implementation Strategy, identity is the new perimeter. If we are dropping network firewalls, we must build unbreakable identity firewalls.
1. Centralized Identity Provider (IdP) Your first technical mandate is consolidating all authentication into a single IdP (like Microsoft Entra ID, Okta, or Ping Identity). If you have legacy apps doing local LDAP authentication, they must be proxied through the IdP using SAML or OIDC.
2. Phishing-Resistant MFA Standard SMS or Authenticator App MFA is dead; attackers bypass them easily using Adversary-in-the-Middle (AiTM) proxy kits like Evilginx. A modern Zero Trust Architecture Implementation Strategy requires FIDO2 WebAuthn (Hardware security keys like YubiKeys or biometrics like Windows Hello/Apple TouchID).
3. Context-Aware Access Policies Authentication is no longer a binary “Yes/No.” It is a dynamic risk score. Your IdP policy engine must evaluate:
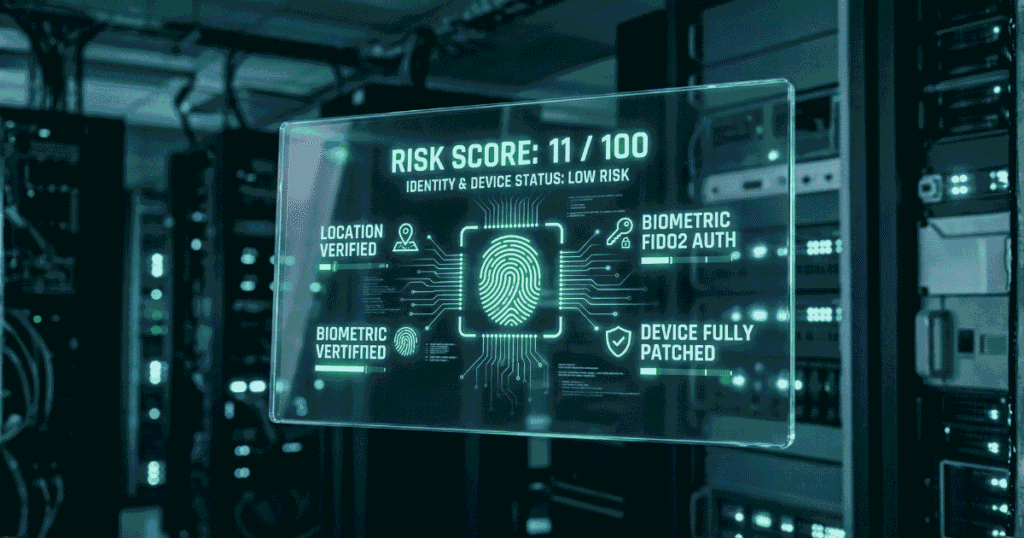
- Who is the user? (Role, Department).
- What is their device? (Corporate issued vs. BYOD).
- Where are they? (Impossible travel detection).
- When are they logging in? (Outside normal behavioral hours).
Example JSON representation of a dynamic Conditional Access Policy block:
JSON
{
"policyName": "Require_Compliant_Device_For_Financial_Data",
"conditions": {
"users": {"includeGroups": ["Finance_Team"]},
"applications": {"includeApplications": ["Salesforce", "Workday"]},
"locations": {"excludeLocations": ["Corporate_HQ_IPs"]},
"clientAppTypes": ["browser", "mobileAppsAndDesktopClients"]
},
"grantControls": {
"operator": "AND",
"builtInControls": [
"mfa",
"compliantDevice"
]
}
}
If any of this context changes mid-session, your Zero Trust Architecture Implementation Strategy must instantly revoke the session tokens.
The Device Pillar (UEM and Posture Checking)
You cannot trust the user if you cannot trust the glass they are touching. A compromised device will simply ride an authenticated user’s session into your data.
A mature Zero Trust Architecture Implementation Strategy integrates Unified Endpoint Management (UEM) with your ZTNA broker. Before the broker grants access to an application, it queries the UEM (like Intune or CrowdStrike) for a “Posture Check.”
Crucial Posture Checks:
- Is the OS fully patched?
- Is the EDR sensor active and reporting no malicious activity?
- Is the firewall enabled?
- Is the hard drive encrypted (BitLocker/FileVault)?
If the CEO’s laptop gets infected with malware, CrowdStrike detects it, changes the device risk score to “High,” and the ZTNA broker automatically severs the CEO’s connection to the financial database in milliseconds. This is the power of an automated Zero Trust Architecture Implementation Strategy.
Network Micro-Segmentation (Stopping Lateral Movement)
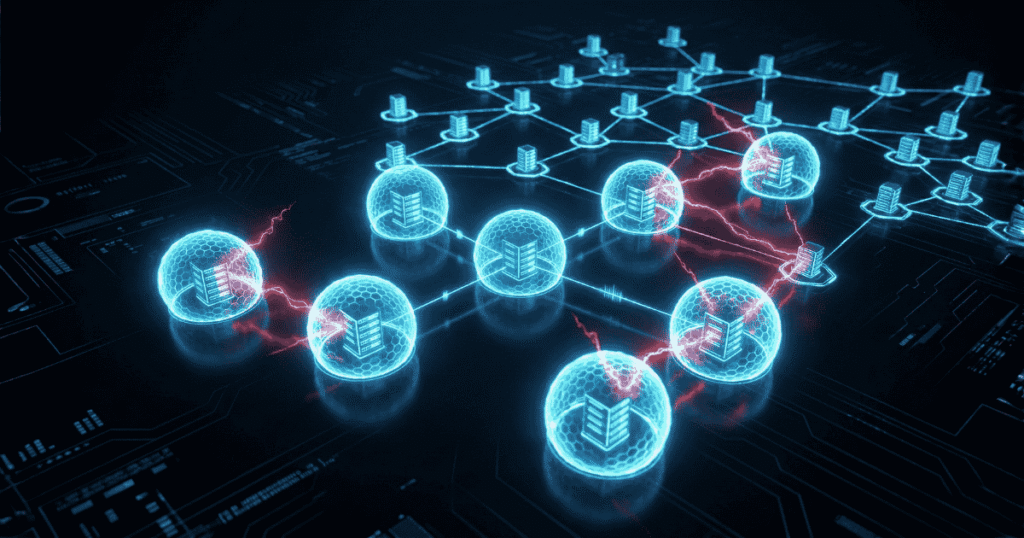
While ZTNA handles the “User-to-Application” traffic, you must also secure “Machine-to-Machine” (East-West) traffic. If a web server is compromised, can it SSH into the database server next to it?
In a flat network, the answer is yes. In a Zero Trust Architecture Implementation Strategy, the answer is no.
Software-Defined Segmentation We no longer use physical hardware firewalls for internal routing. We use host-based micro-segmentation (tools like Illumio or VMware NSX).
- Visibility: You deploy agents to every server (Windows, Linux, Containers). The agents map every single communication flow in your data center.
- Enforcement: You build declarative policies. “Web Server Group A may only communicate with Database Group B over TCP 1433. All other traffic is implicitly denied.”
- The Micro-Perimeter: The enforcement happens at the OS kernel level of the server itself. Even if two servers are on the exact same hypervisor and VLAN, they cannot communicate unless explicitly allowed by the policy.
This ensures that if a vulnerable API endpoint is exploited Opportunity: the blast radius is contained to that single virtual machine.
The 4-Phase Zero Trust Architecture Implementation Strategy
You cannot buy Zero Trust in a box. It is a multi-year journey. Here is the exact phased Zero Trust Architecture Implementation Strategy used by Fortune 500 companies.
Phase 1: Discovery and Surface Mapping (Months 1-3) You cannot protect what you cannot see.
- Inventory every user identity, service account, and third-party vendor access.
- Deploy your micro-segmentation agents in “Monitor Only” mode to map how your applications actually communicate.
- Deliverable: A complete topological map of your protect surface.
Phase 2: Identity Consolidation (Months 4-6)
- Migrate all legacy applications behind your centralized IdP.
- Enforce FIDO2 MFA globally.
- Eliminate persistent VPNs for standard users and deploy the ZTNA client to corporate endpoints.
- Deliverable: A unified authentication plane with context-aware access policies.
Phase 3: Micro-Segmentation Rollout (Months 7-12)
- Switch your segmentation agents from “Monitor” to “Enforce.”
- Start with non-critical workloads to test the friction.
- Segment the “Crown Jewel” databases so only authorized application servers can reach them.
- Deliverable: Complete eradication of lateral movement capabilities within the data center.
Phase 4: Continuous Optimization and CARTA (Month 12+)
- Implement Continuous Adaptive Risk and Trust Assessment (CARTA).
- Integrate your SIEM (Security Information and Event Management) with your ZTNA policy engine to automate session revocation based on real-time threat intelligence.
- Deliverable: An autonomous, self-healing Zero Trust Architecture Implementation Strategy.
Overcoming the Legacy Debt (The Hard Truth)
The biggest roadblock to your Zero Trust Architecture Implementation Strategy will not be technology; it will be legacy debt and organizational friction.
- The Mainframe Problem: You will have legacy AS/400 mainframes or 20-year-old medical devices that cannot install a ZTNA agent and do not understand SAML.
- The Fix: You must build “Enclaves.” Place the legacy device behind a dedicated Zero Trust proxy gateway. The gateway handles the modern authentication and tunneling, then passes the unencrypted traffic the last few inches to the legacy box.
- The Developer Pushback: Developers hate friction. If your Zero Trust Architecture Implementation Strategy breaks their SSH workflows or local container testing, they will find workarounds.
- The Fix: Integrate ZTNA natively into the developer toolchain. Use ephemeral, just-in-time (JIT) certificates for SSH access rather than static keys.
The Vendor Landscape in 2026
To execute this Zero Trust Architecture Implementation Strategy, you must select the right partners. The market has consolidated into Security Service Edge (SSE) platforms:
- Zscaler (ZIA/ZPA): The heavy-hitter for enterprise. Incredible global footprint for ZTNA, but requires heavy architectural commitment.
- Cloudflare (Zero Trust): The king of speed. Excellent for routing and protecting web applications with their massive edge network.
- Palo Alto (Prisma Access): Best if you already have Palo Alto hardware firewalls and want a unified management pane for both physical and cloud security.
- CrowdStrike (Identity Protection): Essential for stopping Active Directory lateral movement and feeding device health telemetry into your ZTNA broker.
Conclusion: The Perpetual State of Verification
A successful Zero Trust Architecture Implementation Strategy fundamentally changes the psychology of an IT department. You stop asking, “Is this person on the network?” and start asking, “Does this identity have the verified context to access this specific byte of data at this exact second?”
Hackers love flat networks, static credentials, and implicit trust. By executing the Zero Trust Architecture Implementation Strategy outlined in this guide, you strip away every advantage the adversary relies upon. You isolate the breach, eliminate lateral movement, and transform your security posture from a brittle perimeter into an adaptable, microscopic fortress.
The perimeter is dead. Long live Zero Trust.
