Introduction: The Reconnaissance Reality
To hunt effectively today, you must build an automated bug bounty reconnaissance workflow. The golden era of pointing a vulnerability scanner at a primary corporate domain and collecting a $5,000 bounty is over. Today, enterprise perimeters are hardened by Web Application Firewalls (WAFs), continuous monitoring teams, and strict Zero Trust policies. If you want to find critical vulnerabilities—whether you are an independent researcher hunting bounties or an internal Red Teamer securing your own perimeter you must find the assets the company forgot they owned. Setting up an automated bug bounty reconnaissance workflow saves hundreds of hours of manual labor.
Success in modern security testing is 80% reconnaissance and 20% exploitation.
Moving past basic certification concepts requires shifting from manual probing to building a scalable, automated pipeline. The goal is no longer to find a bug on a known server, but to discover the forgotten staging server sitting on a legacy IP address with debugging enabled. This comprehensive guide provides a blueprint to mapping the forgotten internet, tracking corporate acquisitions, and finding the hidden endpoints where the critical bugs live.
- Every top-tier researcher relies on a strict automated bug bounty reconnaissance workflow to uncover vulnerabilities.
- Without an automated bug bounty reconnaissance workflow, you are simply wasting time manually probing dead endpoints.
The Mindset Shift Passive vs. Active Recon
Before we touch a terminal, we must define the rules of engagement. An effective methodology is split strictly into two phases: Passive and Active. The distinction is not just semantic; it is the difference between flying under the radar and getting your IP permanently banned by a target’s blue team.”A proper automated bug bounty reconnaissance workflow relies heavily on passive techniques first.
The Passive Phase Passive reconnaissance means you do not send a single packet to the target’s infrastructure. You query third-party databases, historical internet archives, and public registries. It is silent, undetectable, and completely legal regardless of scope. If a company has a wildcard scope (*.company.com), your passive phase will map it without triggering a single alert. Structuring your automated bug bounty reconnaissance workflow into distinct phases prevents early detection by blue teams.The passive phase is the foundation of any successful automated bug bounty reconnaissance workflow.
- Data Sources: WHOIS records, BGP routing tables, DNS dumpsters, Shodan, Censys, and the Wayback Machine.
The Active Phase Active reconnaissance involves interacting directly with the target’s servers. This triggers firewalls, intrusion detection systems, and generates log entries.
- Techniques: Port scanning, DNS brute-forcing, directory fuzzing, and banner grabbing.
Your automated pipeline must always exhaust passive methods to build a massive target list before generating noisy active traffic. Spraying active scans at a single domain is a rookie mistake; selectively targeting the forgotten subdomains you discovered passively is the mark of a professional.
Horizontal Enumeration (Finding the Corporate Umbrella)
Horizontal enumeration expands the scope of your automated bug bounty reconnaissance workflow exponentially. Most hunters start by looking for subdomains of a specific target. This is a fundamental error. A true methodology starts horizontally. You need to find what other companies and infrastructure your target owns. When building your automated bug bounty reconnaissance workflow, horizontal enumeration is the crucial first step. Tracking acquisitions ensures your automated bug bounty reconnaissance workflow always has fresh targets.
1. Autonomous System Numbers (ASN) and IP Space Large organizations do not just rent cloud servers; they own massive blocks of IP addresses routed through their own Autonomous System Numbers (ASN). By identifying a target’s ASN, you can instantly map tens of thousands of IPs they control, regardless of what domain name is attached to them.
- The Process: You can utilize the Hurricane Electric BGP Toolkit (
bgp.he.net) manually, but for automation, we use command-line utilities. - The Execution: ProjectDiscovery’s
asnmaptool allows you to input an organization’s name and retrieve their entire IP landscape in CIDR notation. - Command Line:
asnmap -o "Target Company Inc" -silent > target_cidrs.txt
Once you have the CIDR blocks, you can feed these IP ranges directly into your port scanners later, completely bypassing the need for domain names.
2. Reverse WHOIS & Historical Tracking Companies constantly merge, acquire startups, and rebrand. When Target A buys Startup B, Startup B’s legacy infrastructure is suddenly in scope, and it is almost always poorly secured.
- The Technique: Reverse WHOIS allows you to search for domains based on the registrant’s email address, phone number, or corporate name. If you find the email address
admin@target.comregistered to the main domain, you search the global registry for every other domain registered by that exact email. - Tools: Whoxy API and Crunchbase (for tracking financial acquisitions).
- Automation: By scripting an API call to Whoxy, your pipeline can dynamically add newly acquired domains to your target list the moment a press release announces a corporate buyout.
Vertical Enumeration (The Subdomain Gold Rush)
A deep vertical dive is where your automated bug bounty reconnaissance workflow begins to shine. With our root domains and IP blocks established, we transition to vertical enumeration: digging deep into the subdomains. Integrating Amass into your automated bug bounty reconnaissance workflow is non-negotiable for deep subdomain mapping.
1. Passive Subdomain Gathering Do not brute-force immediately. The internet has already indexed the subdomains for you; you just need to know how to ask.
- Amass: The undisputed heavyweight of passive recon, maintained by OWASP. Amass queries dozens of APIs (like Censys, SecurityTrails, and Shodan) simultaneously.
amass enum -passive -d target.com -o amass_domains.txt
- Subfinder: Built for speed. While Amass builds deep, relational graphs, Subfinder uses Go to rapidly scrape passive sources.
subfinder -d target.com -all -silent > subfinder_domains.txt
- The Master Technique: Never rely on one tool. Run Amass, Subfinder, and
findomain, then concatenate the results and sort them to remove duplicates.cat amass_domains.txt subfinder_domains.txt | sort -u > unique_passive_subs.txt
2. API Key Management Passive tools are only as good as the APIs they query. If you run Subfinder without configuring API keys, you are missing 60% of the results. You must register for free developer accounts at Shodan, Censys, SecurityTrails, and Chaos, and feed those keys into your tool’s configuration files.
3. Active Subdomain Brute-Forcing When the passive well dries up, we pivot to active guessing. We use a lightning-fast DNS resolver to check if a massive list of potential words actually points to a live server. Mass DNS resolution is the engine that drives a fast automated bug bounty reconnaissance workflow.
- The Engine:
purednsorffuf.Purednsis exceptional because it automatically filters out “wildcard” domains (where the server returns a positive result for literally any word you type). - The Ammunition: Your wordlist dictates your success. Do not use default, outdated lists. Pull the highly tuned
jhaddix_all.txtor theraft-large-directorieslists from the SecLists repository. - Execution:
puredns bruteforce wordlist.txt target.com -r resolvers.txt -w active_subs.txt
Permutations and Alterations (The Secret Sauce)
This is where advanced hunters separate themselves from the pack. Companies use predictable naming conventions. If you find dev-api-v1.target.com, there is a high statistical probability that dev-api-v2.target.com or staging-api-v1.target.com exists, even if it has never been indexed by a passive source. Your automated bug bounty reconnaissance workflow must filter out dead hosts quickly to save scanning time. enerating permutations gives your automated bug bounty reconnaissance workflow access to unlinked staging environments.
The Alteration Engine Tools like gotator or altdns take your known subdomains, mash them up with a list of common prefix/suffix words (like dev, test, staging, old, prod), and generate millions of potential new subdomains.
- Feed
unique_passive_subs.txtintogotator. - Generate 5 million possible variations.
- Feed that massive list back into
purednsto resolve them.
This technique consistently uncovers hidden administrative portals that internal teams believed were secret simply because they weren’t linked anywhere on the internet.
Resolving and Service Fingerprinting
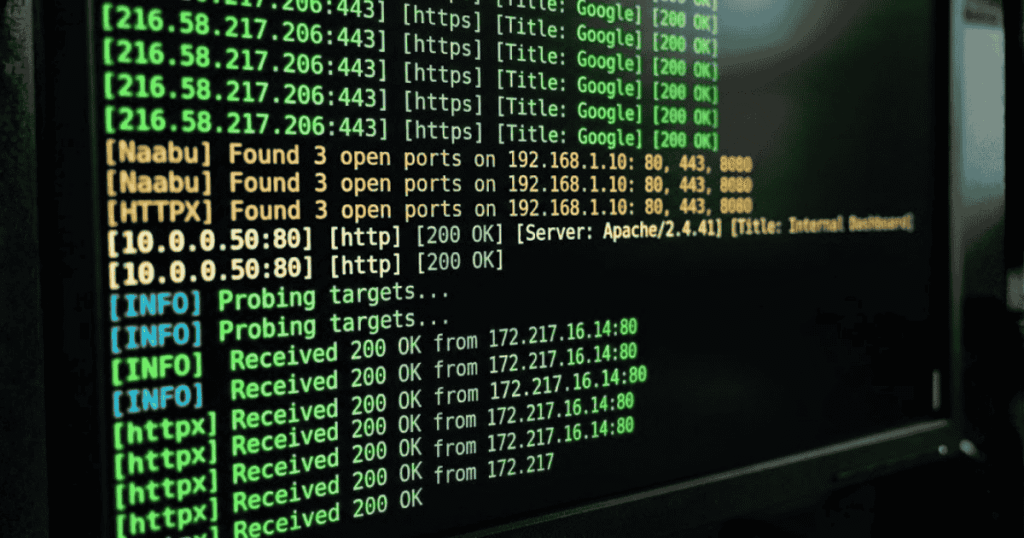
You now have 50,000 resolved subdomains. However, a resolved DNS record just means an IP address exists. It does not mean a web server is running. A highly tuned pipeline filters this noise instantly.
1. Mass Web Probing with HTTPX We need to know which of those 50,000 domains respond to web requests on common ports (80, 443, 8080, 8443). We use ProjectDiscovery’s httpx to probe the list concurrently.
- The Command:
cat all_resolved_subs.txt | httpx -silent -ports 80,443,8080,8443 -title -tech-detect -status-code -o live_web_hosts.txt - The Output: This command doesn’t just verify the host is alive. The flags
-titleand-tech-detectpull the page title and the underlying technology (e.g., “Apache”, “React”, “WordPress”). You can immediately grep the output for titles like “Admin Dashboard” or “Jira Setup”.
2. Port Scanning at Scale Standard Nmap is far too slow to scan 50,000 hosts. We use a two-step approach.
- Step 1: Use
NaabuorMasscanto rapidly identify open ports across all hosts at extreme speeds. - Step 2: Pipe only the confirmed open ports into Nmap for deep service fingerprinting (version detection and script scanning).
- Execution:
naabu -l all_resolved_subs.txt -p - -silent | awk -F ':' '{print $1}' | sort -u > ports_open.txtnmap -iL ports_open.txt -sV -sC -T4 -oN nmap_detailed_scan.txt
Endpoint & JavaScript Analysis (The Hidden Layer)
Finding the server isn’t enough; you need to find the specific files and hidden API paths on that server. Extracting hidden JavaScript paths gives your automated bug bounty reconnaissance workflow a massive edge over other hunters. Parsing JavaScript files manually is impossible, so it must be handled by your automated bug bounty reconnaissance workflow.
1. Historical URL Scraping Before sending packets, ask the internet what URLs used to exist on this server years ago.
- Tools:
waybackurlsorgau(Get All URLs). - Execution:
cat live_web_hosts.txt | gau > historical_urls.txt - The Value: You will often find endpoints like
/api/v1/user_exportthat are no longer linked on the modern website, but the backend code still blindly accepts requests.
2. JavaScript Parsing Modern web applications (built on React, Angular, or Vue) handle routing on the client side. This means the frontend .js files sent to your browser contain a hardcoded map of the entire backend API.
- The Technique: Use tools like
KatanaorLinkFinderto crawl the live web hosts, download every JavaScript file, and use regular expressions to extract every hidden path mentioned in the code. - Execution:
katana -list live_web_hosts.txt -jc -kf -d 3 > endpoints.txt
Once you find these endpoints, you must test them for broken authentication. Many of these are legacy routes exactly the kind of threats detailed in my recent breakdown of Zombie APIs.
Scripting the Automated Bug Bounty Reconnaissance Workflow
A workflow is only “automated” if it runs while you sleep. To build this out, you need a Virtual Private Server (VPS) running Linux and a robust Bash script to glue these tools together. You can host your entire automated bug bounty reconnaissance workflow on a cheap $5 Linux VPS
The Master Recon Script Architecture: Do not copy-paste code blindly; understand the flow. A professional script creates organized directories, runs tools concurrently, and cleans up its own temporary files.
Bash
#!/bin/bash
TARGET=$1
DATE=$(date +%Y-%m-%d)
mkdir -p recon/$TARGET/$DATE
echo “[+] Starting reconnaissance pipeline for $TARGET”
# Step 1: Horizontal ASN Mapping
echo “[*] Mapping ASN…”
asnmap -d $TARGET -silent > recon/$TARGET/$DATE/cidrs.txt
# Step 2: Passive Subdomain Gathering
echo “[*] Harvesting passive subdomains…”
subfinder -d $TARGET -all -silent > recon/$TARGET/$DATE/subfinder.txt
amass enum -passive -d $TARGET -o recon/$TARGET/$DATE/amass.txt
cat recon/$TARGET/$DATE/subfinder.txt recon/$TARGET/$DATE/amass.txt | sort -u > recon/$TARGET/$DATE/unique_subs.txt
# Step 3: Resolving Live Hosts
echo “[*] Probing for live web servers…”
cat recon/$TARGET/$DATE/unique_subs.txt | httpx -silent -ports 80,443 -title -sc > recon/$TARGET/$DATE/live_hosts.txt
# Step 4: Vulnerability Scanning (Low-Hanging Fruit)
echo “[*] Running template scans…”
cat recon/$TARGET/$DATE/live_hosts.txt | awk ‘{print $1}’ | nuclei -t cves/ -t exposed-panels/ -silent -o recon/$TARGET/$DATE/vulns.txt
echo “[+] Pipeline complete. Results saved in recon/$TARGET/$DATE/”
This is the foundational skeleton. To make it enterprise-grade, you would add error handling, multi-threading using tools like interlace, and parsing logic to automatically flag high-value targets.
Continuous Monitoring (The Ultimate Advantage)

Continuous monitoring is the ultimate crown jewel of a modern automated bug bounty reconnaissance workflow. The internet is dynamic. A DevOps engineer might spin up a testing server without a password on a Tuesday afternoon and tear it down by Wednesday morning. If your script only runs on weekends, you miss the vulnerability entirely.
Cron Jobs and Diffing The final piece of the puzzle is continuous execution.
- Set your Bash script to run every 24 hours via a Linux
cronjob. - Use the
anewtool (created by Tomnomnom).anewcompares yesterday’s text file to today’s text file and outputs only the new lines. - Pipe those new lines into a notification tool like
notify.1
When configured correctly, your phone will receive a Slack or Discord message alerting you: “New Subdomain Detected: https://www.google.com/search?q=dev-database.target.com”. You are now attacking fresh, unsecured infrastructure within minutes of it going live on the internet, beating out thousands of other researchers.
Conclusion: Discipline Over Tools
Tools will inevitably change. Amass might be deprecated tomorrow, and a new scanner will take its place. But the methodology behind this architecture is permanent.
Understanding horizontal correlation, vertical enumeration, rapid resolution, and continuous monitoring proves you possess a senior-level grasp of network architecture. Stop competing with the crowd on the primary domains. Build your automation, map the dark corners of the network, and secure the invisible attack surface before the adversaries do.
Ultimately, an automated bug bounty reconnaissance workflow is what separates amateurs from professionals. Master your automated bug bounty reconnaissance workflow, and the hidden bugs will reveal themselves.
Start building your automated bug bounty reconnaissance workflow today to stay ahead of the competition. A well-maintained automated bug bounty reconnaissance workflow will consistently yield higher bounties than manual testing.
For more tutorials on building secure infrastructure and mastering the command line, explore the latest technical guides on oxofel.com.
