Introduction
It is Monday night. Your team is anxious. Why? Because tomorrow is “Patch Tuesday,” and in most organizations, that means chaos. It means scrambling to read CVE lists, frantically testing updates, and praying that a server doesn’t crash. But it doesn’t have to be this way. The difference between a crisis and a routine operation is a proactive patch management strategy.
In 2026, the speed of weaponization has accelerated. Hackers are exploiting vulnerabilities within 48 hours of disclosure according to the CISA Known Exploited Vulnerabilities Catalog. If you are waiting for the vendor to tell you what to fix, you are already too late. A proactive patch management strategy is not just about installing updates; it is about “Governance by Design.” It is about knowing your environment so well that when a vulnerability drops, you already know the impact. In this guide, we will dismantle the old “reactive” model and build a bulletproof proactive patch management strategy that keeps your infrastructure secure and your sanity intact.
The Cost of Being Reactive in Proactive Patch Management Strategy
Why is the old way failing? Because it relies on “Implicit Trust.” You trust the vendor to release a working patch, and you trust your network to accept it. But in 2026, patches break things. Without this, you are gambling. You are deploying untested code into production environments under the gun of a Zero-Day threat. This leads to downtime, operational friction, and burnout. A true proactive patch management strategy flips the script: we prepare the battlefield before the enemy arrives.
Phase 1: Asset Intelligence (Know Your Terrain)
You cannot patch what you do not know. The foundation of any proactive patch management strategy is a real-time, dynamic inventory.
- Shadow IT Discovery: Your proactive patch management strategy must include automated scanning aligned with the NIST Guide to Enterprise Patch Management.(using tools like Wazuh or Nessus) to find unmanaged assets.
- Dependency Mapping: It’s not just the OS; it’s the libraries. Does your billing app rely on a specific version of Java? A proactive patch management strategy documents these dependencies so you know exactly what will break if you update Java.
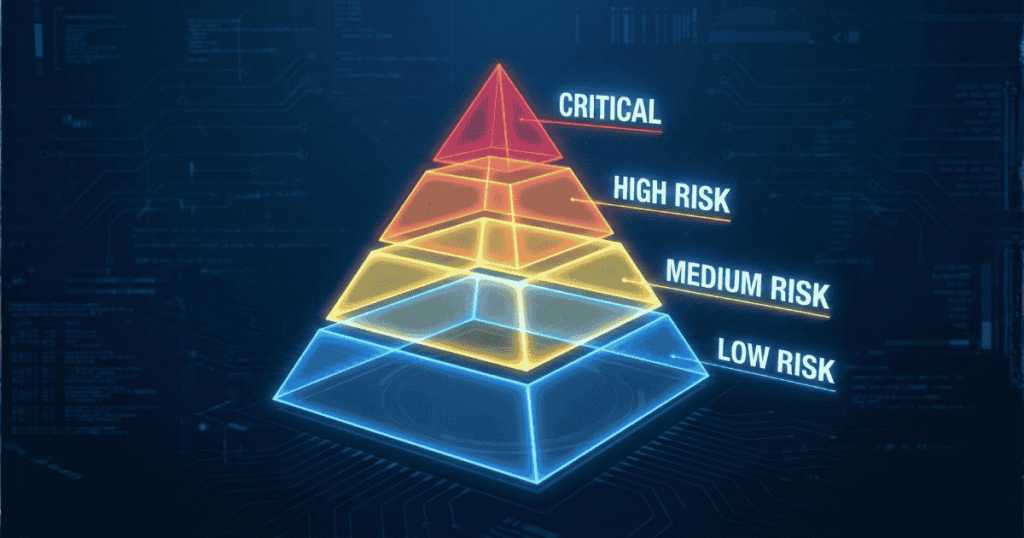
Phase 2: The “Triage” Protocol
Not all patches are created equal. A core tenet of a proactive patch management strategy is “Risk-Based Prioritization.”
- CVSS is not enough: A Critical (9.8) vulnerability on a server that is air-gapped is less dangerous than a Medium (5.0) vulnerability on your public web server.
- Contextual Scoring: Your proactive patch management strategy must weigh the “Exploitability” (is there code in the wild?) against “Business Impact” (will this crash the CEO’s laptop?).
Phase 3: The “Sandbox” Standard
Never deploy to production first. That is the cardinal sin of a proactive patch management strategy.
- The Ring Model: Deploy to “Ring 0” (IT Team) first. Then “Ring 1” (Power Users). Finally “Ring 2” (General Population).
- Automated Rollback: Part of your proactive patch management strategy must be the “Undo Button.” If a patch causes a memory leak in Ring 1, the system should automatically revert the changes.
Phase 4: Verification and Compliance
Installing the patch is not the end. Verifying the fix is where a proactive patch management strategy shines.
- Rescan Immediately: Don’t assume it worked. Run your vulnerability scanner immediately after the reboot.
- Compliance Reporting: Auditors love a proactive patch management strategy. They want to see the “Time to Remediate” (TTR) metrics. How fast did you go from “Disclosure” to “Patched”?

My Take: Governance Over Tools
You can buy the most expensive tools in the world, but without a proactive patch management strategy, they are useless. I have seen teams with million-dollar budgets get hacked because they didn’t have a process for patching a third-party plugin. Your proactive patch management strategy is a cultural shift. It moves your team from “Firefighters” to “Fire Marshals.” You stop fighting fires because you stopped them from starting.
Conclusion
The chaos of Patch Tuesday is a choice. By adopting this strategy, you regain control. You protect your data, you stabilize your uptime, and you sleep better on Monday nights. The threats of 2026 are fast, but a well-oiled proactive patch management strategy is faster. Start building your inventory today, categorize your risks, and turn patching from a panic into a process.
Want to know which tools help automate this? Check out my guide on the oxofel.com best open source scanners.
